While they offer attractive proximity, dating apps hide serious privacy risks. A concept that can almost be an illusion.
The relationship may start long distance, but in the world of online dating, geographic proximity has become an increasingly important criterion. Users can, thanks to location data, identify potential partners a few kilometers or hundreds of meters from home. But, and this is a bit of the other side of the coin, the functionality presents risks for the privacy but also for the security of members of dating applications.
Even if protective measures exist, dating app users remain prone to trilateration
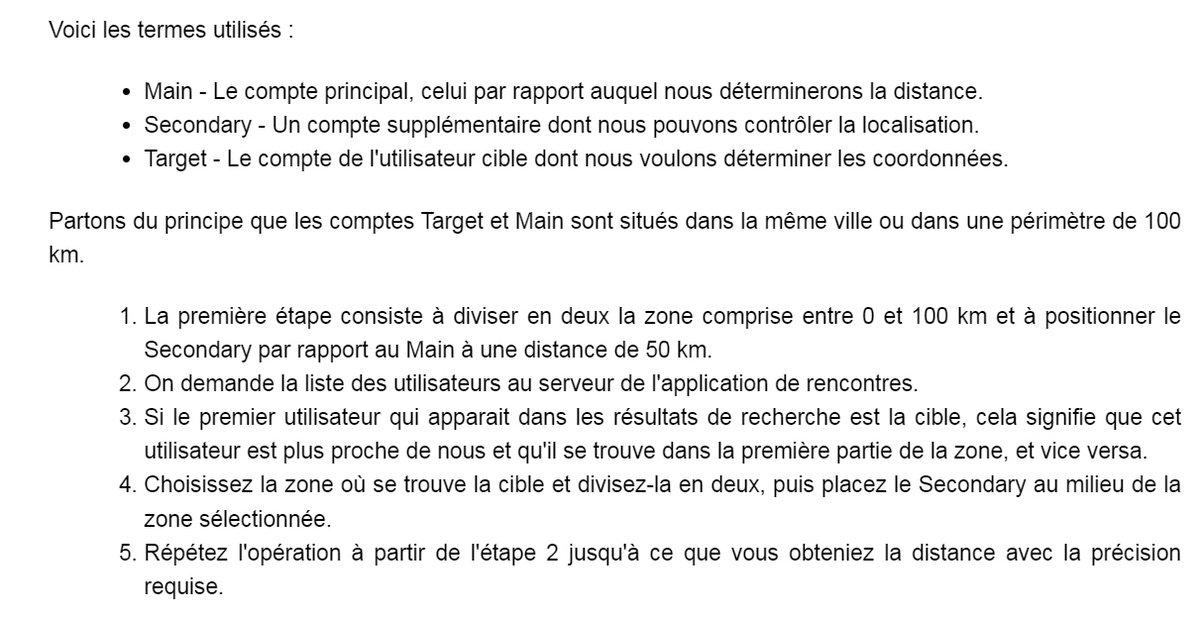
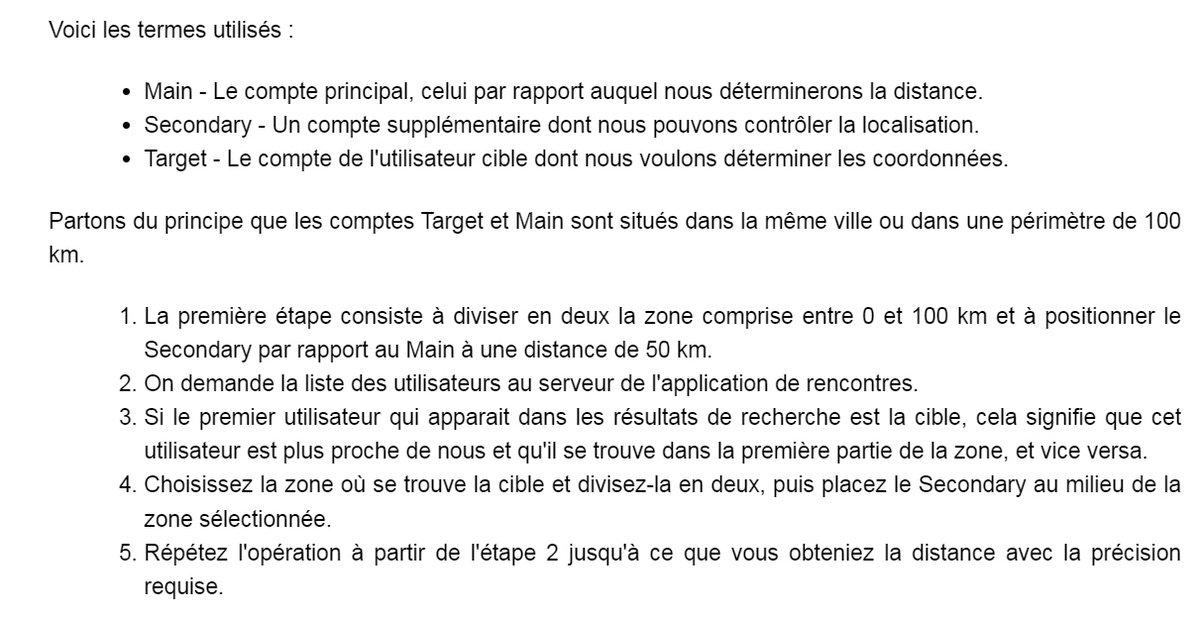
To connect users, dating applications rely on geolocation. The practice exposes users to security risks, such as trilateration. This technique helps determine the exact location of a person by analyzing location data from different sources. In other words, we base ourselves on the coordinates of several points and the distance between them.
Malicious individuals can exploit this information to track users and follow their movements. Registered members are then under threat, whether with regard to their private life or their physical integrity. The individuals in question must still have certain technical skills, such as trilateration.
Developers of applications of this type have taken steps to protect users’ geolocation data. We can mention the approximation of geographic coordinates, the random modification of the distances displayed, as well as the possibility for users to hide their exact position. But all these precautions are not enough to plug the gaps.
Calculating the distance between different users is possible
An analysis of two popular dating apps reveals quite divergent practices when it comes to geolocation security. The first uses a coding system (in the form of a 12-digit geohash) to reduce location precision by rounding geographic coordinates to the third decimal place.
The second, Hornet, sends precise coordinates to the server. She defends herself by explaining that she protects users’ positions thanks to the random nature of the distance displayed in the application. Depending on the application, this makes it difficult to determine the exact location. It is nevertheless possible to deactivate the location function from your profile. Note that it is largely thanks to the cyber experts at Check Point Research that the application added this functionality.
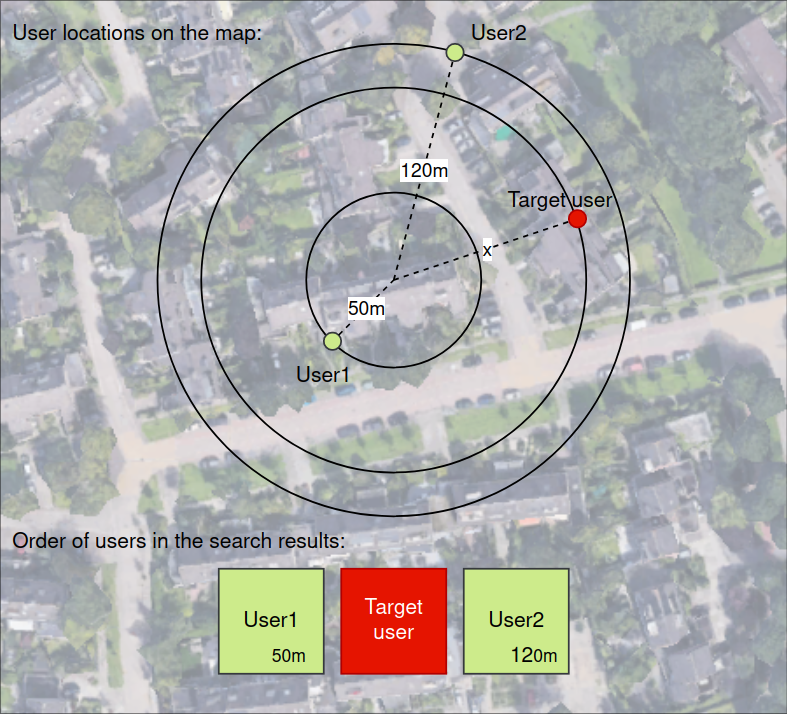
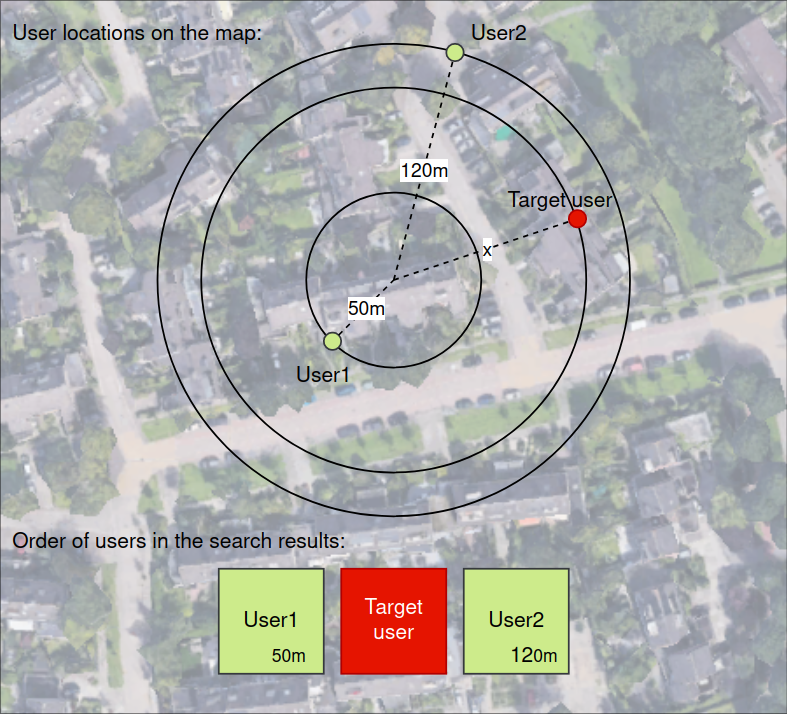
Check Point shows that on the Hornet app, if two users well positioned in the app’s search results agree to share their location, and the target user is between them in these results, we can definitely make an estimate of the distance to the target user, by calculating the average of the two known distances. However, it is not necessary to have other members nearby. Creating an additional account whose location can be controlled may be sufficient.
After following the traditional responsible disclosure procedure, the research team attempted to contact Hornet to share the results of their study. She did not receive a response. However, just before the findings were released, a reassessment of the app showed that steps had been taken to reduce the accuracy of users’ contact details, although there was no more detailed response from the development team.
Pay attention to the permissions granted to dating apps: basic advice
Detailed examination of the Hornet application revealed several peculiarities in the management of location data. For example, the app developers randomly change the distance displayed between user profiles at the server level, which limits location accuracy.
Add to this that a trilateration method was used to determine distances with greater precision. This method consists, remember, of using several reference points to estimate the position of a user, which could be used to circumvent the security measures put in place by the application.
In any case, these discoveries clearly show the issues linked to the protection of privacy in dating applications. All of this highlights the importance of users understanding the risks associated with geolocation. This is why Check Point Reseach recommends that users carefully review the permissions granted to applications, and take measures to protect their privacy, in particular by deactivating location services as soon as possible.


11