This is how you can check immediately whether your email address has been leaked on the Internet. How to react correctly if you are affected.
Enlarge
How to check if your email address is being misused
© Ekateryna Zubal/Shutterstock.com
With these free online tools, you can immediately check whether your email address has been leaked on the Internet and appears in connection with stolen data.
haveibeenpwned by Troy Hunt
On haveibeenpwned you can have your e-mail address checked by the operator Troy Hunt to see whether it appears on the Internet in connection with leaked data. The page immediately shows you the result of the verification. See the screenshot below:

Enlarge
This is what it looks like when haveibeenpwned.com returns the result for an email address that was discovered on the Internet in connection with data leaks.
The result gives tips on how to improve the security of the affected mail account and explains in which breaches your mail password was discovered. The site also offers the option of checking phone numbers to see if they appear in breaches. You can also search for stolen passwords. You can also be notified automatically if your email address stored with haveibeenpwned appears in a breach.
Important:
Even if your email address doesn’t appear in any data leaks, that doesn’t mean it hasn’t already been hacked or isn’t easy to hack – for example because of a weak password. On the other hand, it does not necessarily mean that your email address is already being misused if it is contained in a breach.
Operator Troy Hunt is an executive at Microsoft in Australia. He also runs one
twitter channel
on data leaks on the web.
HPI Identity Leak Checker from the Hasso Plattner Institute for Digital Engineering gGmbH
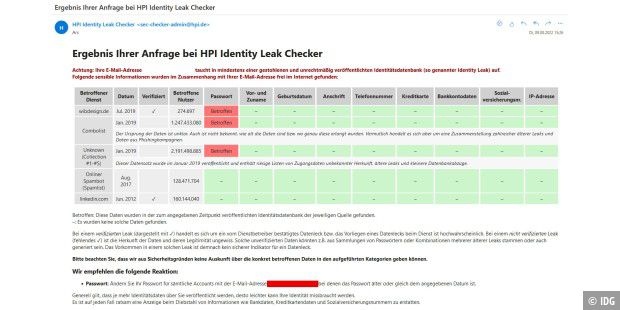
The HPI Identity Leak Checker is another free online tool that you can use to check your email address for leaks. The result of the check is not displayed directly on the HPI Identity Leak Checker website, but instead the HPI Identity Leak Checker sends an email with the result of the check to the checked email address, see screenshot:
Enlarge
This is what the email that HPI Identity Leak Checker sends to the checked email account looks like.
The operator here is the Hasso Plattner Institute (HPI) of the University of Potsdam. See the FAQ for details on how it works. Important: “The Identity Leak Checker only provides information as to whether your password was found in a leak. The Leak Checker does not say anything about whether this password still works for the affected user account. Because your password can still be found in the corresponding leak , the website continues to issue a warning.”
How to react correctly
If the above tools show you that your email address appears in data leaks/breaches, then you should change the password for it immediately. If you have used the same password that you use for your mail account for other services, you should change this password there as well.
Experts: How to find a really strong password
Very important:
Install two-factor authentication if it is supported for your mail account.
If necessary, use a password manager like LastPass to create and save a password that is as secure as possible.
The best password managers in the test 2022
Where did the stolen email addresses come from?
Most stolen e-mail addresses come from attacks on company servers running services that you have registered with with your e-mail address. For example, as it became known in July 2022, cyber gangsters stole the data from several hundred thousand customers of the Hessian energy supplier Entega. These treasures of data are then offered for sale by the thieves in Internet forums or on the dark web. Other major enterprise-level data breaches include:
Facebook data stolen: Here you can see if you are affected
Mega leak: 773 million email addresses on the web
500 million LinkedIn user data on the web – that’s what LinkedIn says about it
Class action lawsuit: Ashley Madison compensates hack victims
Hackers blackmail Sony Pictures with stolen files
A data theft that happened some time ago but was very spectacular at the time: In 2011, cyber gangsters stole the data from around 160 million Sony customers.
You are powerless against such data leaks caused by server data stealing, you cannot prevent them.
