Behind the remote maintenance technology “Integrated Lights-Out” (iLO) developed by Compaq and used by Hewlett Packard Enterprise (HPE), as with most such server components, there is a separate computer that can be reached via the network. He can remotely control the server and not only switch it on and off, but also operate it remotely, install operating systems and even update its firmware. The iLO can be accessed via a separate network card, but also from an installed operating system. The function cannot be switched off, but is active as soon as a server receives power.
The malware tricked the update function
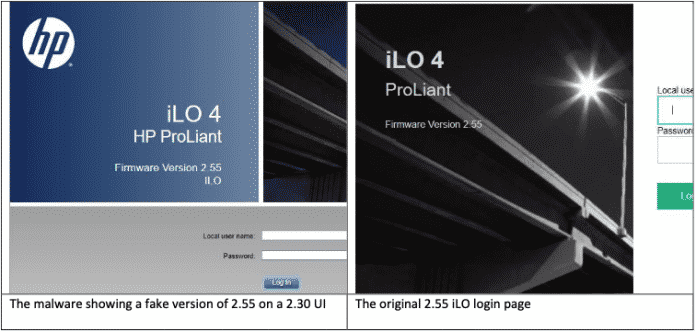
iLO allows remote maintenance of a server from the browser. The security researchers discovered that the malware forged the version number on the login page, but did not reproduce the visual change made by HP.
(Image: Report from Amnpardaz)
The “Implant.ARM.iLOBleed.a” malware in the HPE-iLO firmware analyzed by Amnpardaz was built in such a way that it regularly deleted all data carriers on the server. So even if an admin set up the server again, the intruder would destroy his work again after a while. According to Amnpardaz, updates to the iLO firmware cannot harm the malware: it tricked the update function by reporting that it was successful. On top of that, he manipulates the version number that is displayed on the web interface. Admins feel like they are in a false sense of security.
In their detailed paper, the discoverers tear apart how the malware settles in iLO. Among other things, it shuts down the mechanisms provided by HPE that check the signatures of the loaded modules. For the investigation, the discoverers developed their own tools to read the iLO firmware from the installed operating system of a server; HPE only provides tools to update them from there. In addition, a network scanner was created that takes advantage of security gaps in iLO 2.30 to 2.50. The explorers still want to publish the tools.
The published paper contains the usual instructions for securing iLO and other remote maintenance technology for servers: This should only be accessible in isolated, local networks. Passwords for remote access should be changed and assigned individually. The iLO firmware should always be current. In modern versions (from G10 servers) the firmware downgrade should be prohibited (older versions allow that, which is another little trickery). And: admins should be aware that malware can also sit in the iLO.
(ps)
