The new version of this little-known ransomware, but one of the most popular among hackers, is raising the concerns of specialists. This update brings it under the antivirus radar.
You probably don’t know it, however, it has existed since 2018. It is hackers’ favorite ransomware which has ultimately evolved very little since its creation. It’s called STOP and just recently its update alerted researchers at Sonic Wall, an American cybersecurity company.
Indeed, the latest version discovered deploys the ransomware in several stages, which makes it undetectable by antiviruses. Although STOP does not steal personal data and the ransom amounts are rather low, it is especially worrying because of the large number of victims it can cause.
STOP deployment in several stages
Initially, the ransomware begins its infiltration by loading a seemingly innocuous DLL file, such as msim32.dll, presumably in an attempt to divert attention. It runs extended timer loops in parallel to bypass time-based security measures, making malware detection more difficult.
Then it deploys API calls to allocate the necessary memory space with read/write and execute permissions. This approach makes it even more difficult to detect malicious activity because it avoids more predictable memory allocation patterns.
The next step is to dig into legitimate processes, hijacking their normal operation to inject its own payload into memory. This subtle manipulation is achieved through a series of carefully orchestrated API calls, enabling discrete and memory-efficient execution.
Once this final payload is executed, additional actions are taken to ensure the ransomware persists, such as modifying access control lists (ACLs) to prevent users from deleting malicious files and creating a task scheduled to run the payload regularly. The files are encrypted and a “.msjd” extension is added to their new names.
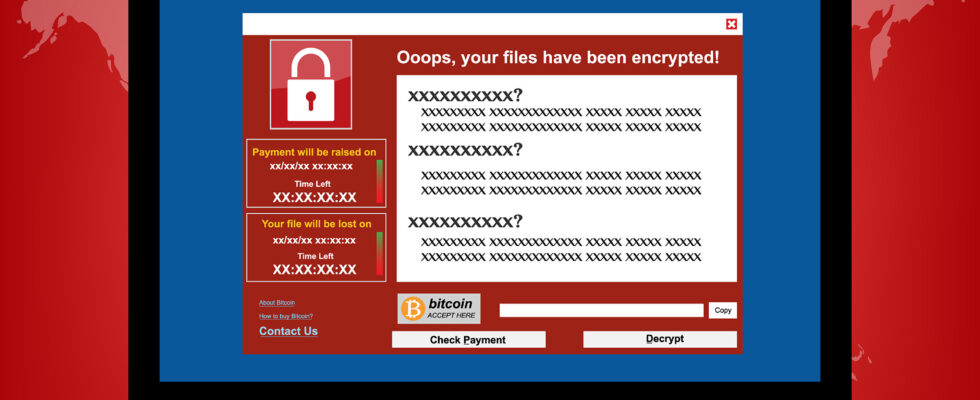
Finally, a ransom note named “_readme.txt” is created in each affected folder, giving victims instructions on paying the ransom for data recovery.
A discreet yet devastating ransomware
Also known as StopCrypt or STOP DJVU, it is one of the most widespread ransomware and for good reason, unlike other ransomware which targets large companies, this one attacks ordinary users by requesting several small ransoms rather than a very large sum at once.
Furthermore, it receives very little media attention due to the fact that its victims very rarely complain about having been ransomed. Indeed, STOP is very often distributed through malicious advertisements, illegal websites and dark web forums. Victims usually search for pirated commercial software, activators, game cheats, etc. They therefore prefer not to brag about having been infected.

Finally, it is often the multi-million dollar ransoms targeting large companies or organizations that are highlighted in the media, such as very recently the LockBit gang, which continues to taunt the highest authorities and claim victims. At the beginning of March 2024, two gangs even joined forces in a large ransomware attack across 15 countries.
StopCrypt was first discovered in 2018. Yet its developers haven’t done much over the years to expand its functionality, as most updates simply fixed critical issues.
Source : Bleeping Computer, Sonic Wall

0