If you have installed software anti-virus on your PC or smartphone (excellent idea!), you can ask yourself the question of how it works? Let’s take a look under the hood of antiviruses to understand how they work and why you need to install an antivirus!
Viral signatures: you will have the basics
When working properly, a security suite or free antivirus should be able to identify and block a virus. How do they do it? The first level is signature recognition. Like any file, a virus is made up of bytes. Generally, we speak of a “byte” (or octet) for 8 bits, but its size can in fact be between 1 and 48 bits.
A site like Fileformat.info allows you to create a “dump” and display a file as a series of bytes, represented in hexadecimal format. This will bring back memories for the oldest among you.
The signature of a file is a series of successive bytes which is specific to it and which allows it to be identified. It is not an exact science, but it is possible to recognize recurring patterns in one or more malware, and thus detect them.
The signature database brings together all the signatures of known malware at a given time. It has long been the only component allowing the detection of a virus or malware. The simple description of how it works is enough to identify its shortcomings: for malware to be detected by this process alone, it must already be known.
Over the past ten years, the methods for updating these signature databases have improved considerably, notably using “push” techniques to offer new signatures to the user as quickly as possible, rather than updates. regularly at more distant intervals.
Enlisting the help of users to detect malicious files via the Cloud has also contributed to the acceleration of the availability of virus signatures. However, signature databases, if they are still used, are only one of the components of modern protection.
Under the engine hood
It is in this context that we speak of an analysis engine. The engine brings together all the technologies necessary for the detection and removal of malware. This includes the signature base, but also the components necessary for other more modern techniques, such as heuristic or behavioral analysis. Here, we will no longer simply detect known files but analyze their behavior in the system, which makes it possible to overcome the limitations of the signature base, and thus also detect threats which have not yet been identified.
Heuristic analysis can involve “decompiling” a malicious file to analyze it and compare its structure to already known codes, looking for similarities that can identify it as a new, unknown threat. Another more complex method runs the file in a sandbox, looking for suspicious behavior.
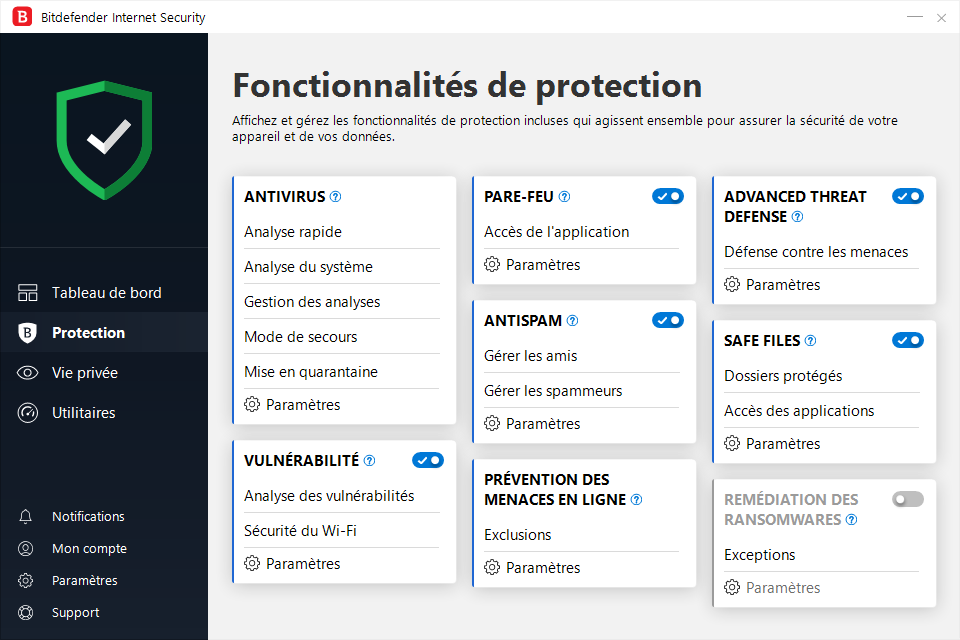
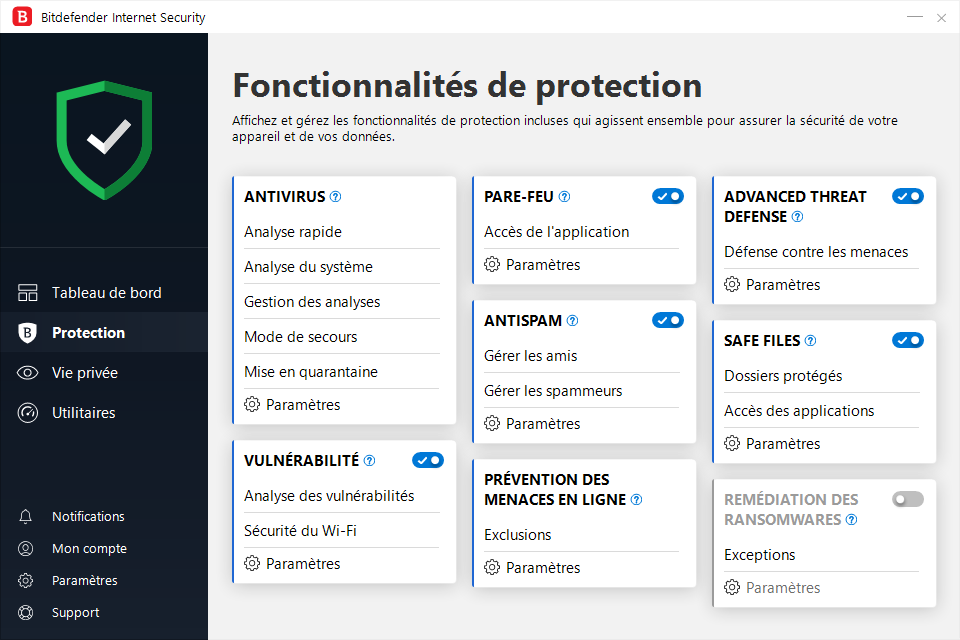
So-called behavioral analysis monitors the operating system for known suspicious behavior, such as abnormal file modifications. The behavior is then blocked by the antivirus. The antivirus engine will thus include components such as an emulator allowing the malicious code to be executed in a secure environment, an archive decompression module, or even an unpacker responsible for dissecting the executable files.
A central but modular component
The engine of an antivirus or security suite is designed to be modular. It is at the heart of all a publisher’s solutions and we must be able to add other components and the user interface to it. However, while a “basic” antivirus, a security suite or a “total security” solution have different functionalities, they all use the same engine.
Some security software publishers also sell their engines as white labels, so they can be found in several solutions from different publishers. A security suite can even use two engines – alternatively or in combination – to optimize its detection and removal of malicious files.
A question about antiviruses? Our explanations
- What do an antivirus and security suite protect me from?
- How does an antivirus detect a virus?
- How antiviruses increase their defenses against hackers
- Why do antivirus companies offer crypto mining services?
1

Bitdefender
-
mood
30 day trial
-
devices
3 to 10 devices
-
phishing
Anti-phishing included
-
local_atm
Anti-ransomware included
-
groups
Parental controls included
9.5
See the offer
2

Norton360
-
mood
14 day trial
-
devices
10 devices
-
phishing
Anti-phishing included
-
local_atm
Anti-ransomware included
-
groups
Parental controls included
9.3
See the offer
3

Avast One
-
mood
30 day trial
-
devices
5 to 30 devices
-
phishing
Anti-phishing included
-
local_atm
Anti-ransomware included
-
groups
No parental controls
9.2
See the offer


0